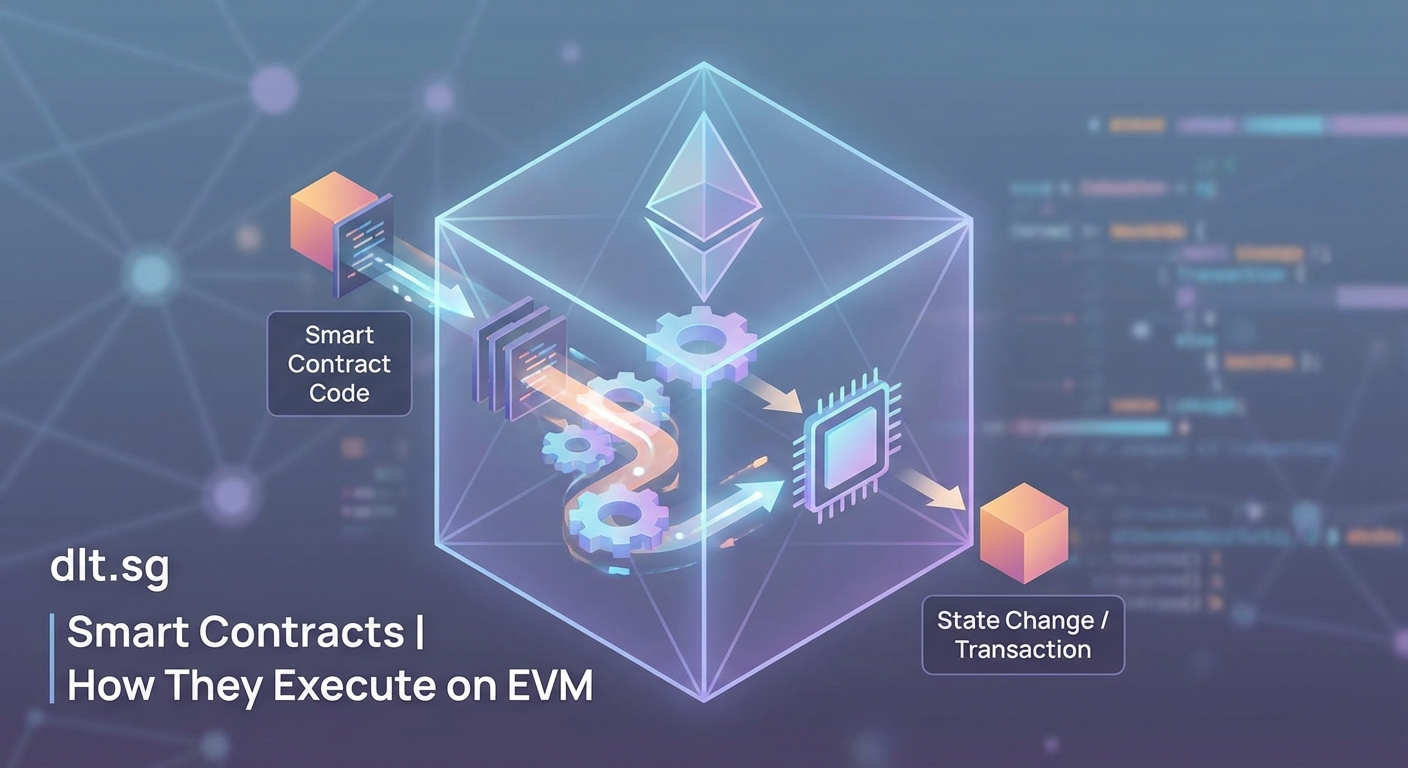
When you deploy a smart contract to Ethereum, you’re not just uploading code to a blockchain. You’re feeding instructions into a distributed computation engine that thousands of nodes will execute identically, deterministically, and verifiably. Understanding how smart contracts execute on Ethereum means peeling back the abstraction layers to see what actually happens inside the Ethereum Virtual Machine.
Smart contracts execute on Ethereum through a multi-step process: Solidity code compiles to bytecode, which gets stored on-chain. When called, the EVM loads this bytecode, processes opcodes sequentially, consumes gas for each operation, and updates state. Every node runs the same instructions identically, creating deterministic consensus across the network. Understanding this execution flow helps developers write efficient, secure contracts that minimize gas costs and avoid runtime failures.
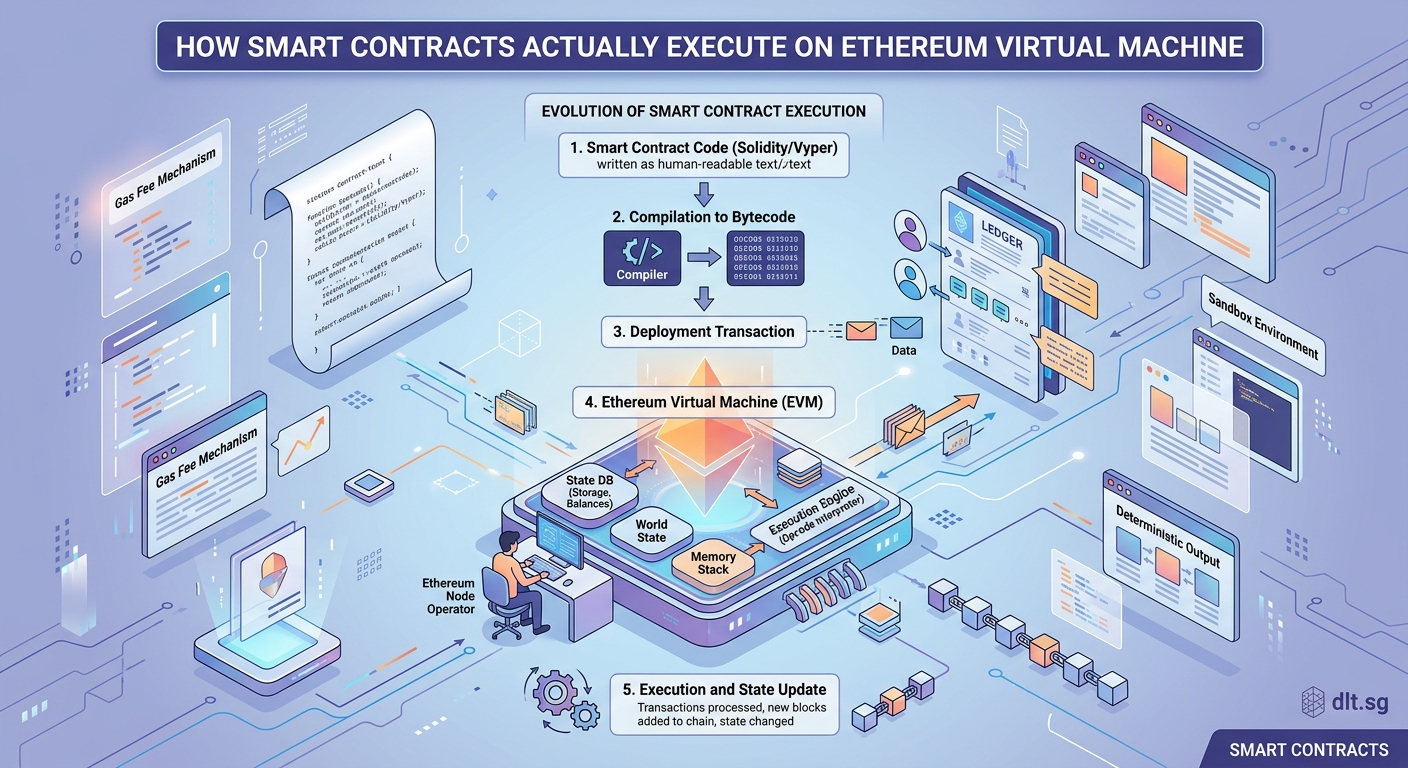
From Solidity to Bytecode
Your smart contract starts as human-readable Solidity code. But the EVM doesn’t understand Solidity.
It only processes bytecode.
The compilation step transforms your high-level contract into low-level instructions. The Solidity compiler outputs two critical pieces: the bytecode that gets deployed on-chain, and the Application Binary Interface (ABI) that external applications use to interact with your contract.
Bytecode is a sequence of hexadecimal values. Each byte or pair of bytes represents an opcode, the fundamental instruction the EVM can execute. When you see 0x6080604052... in a deployed contract, you’re looking at these opcodes in their raw form.
The compiler also performs optimization. It can inline functions, remove dead code, and reorder operations to reduce gas consumption. Different optimization levels produce different bytecode from identical Solidity source.
Once compiled, this bytecode gets packaged into a transaction. Deploying a contract means sending a transaction with the bytecode in the data field and no recipient address. The network processes this special transaction type and assigns your contract a permanent address.
The EVM Runtime Environment
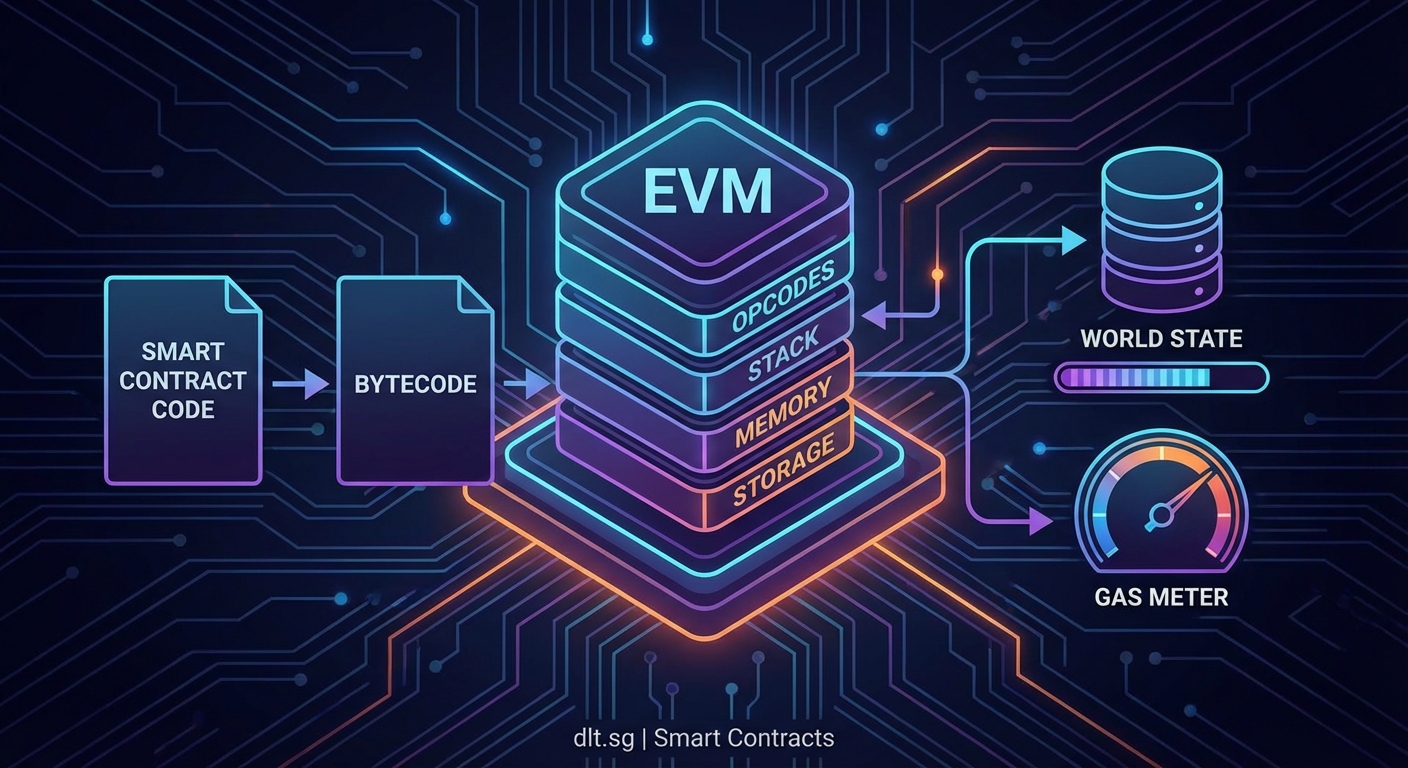
The Ethereum Virtual Machine is a stack-based computation engine. It doesn’t have registers like traditional CPUs.
Instead, it maintains a stack where operations push and pop values.
Every node running Ethereum software includes an EVM implementation. When a transaction calls your contract, every validating node loads the bytecode and executes it in an isolated environment. This isolation prevents contracts from accessing node resources or interfering with other contracts beyond defined interaction patterns.
The EVM provides several data locations:
- Stack: Temporary workspace for operations, maximum 1024 items deep
- Memory: Volatile byte array that expands as needed during execution
- Storage: Persistent key-value store that survives between calls
- Calldata: Read-only input data from the transaction
Understanding these locations matters because accessing them costs different amounts of gas. Storage operations are expensive because they modify the permanent blockchain state. Memory operations cost less but still scale with usage. Stack operations are cheapest.
The EVM also maintains a program counter that tracks which opcode to execute next. Most operations advance the counter by one, but jump instructions can redirect execution flow for loops and conditional logic.
Step-by-Step Execution Flow
Here’s what happens when someone calls your deployed contract:
- A user or another contract sends a transaction specifying your contract address and function call data.
- The transaction enters the mempool and gets included in a block by a validator.
- Every node processing that block loads your contract’s bytecode from state storage.
- The EVM initializes the execution context with the caller’s address, sent value, gas limit, and input data.
- The program counter starts at position zero in the bytecode.
- The EVM reads the opcode at the current position and executes the corresponding operation.
- Each operation consumes a predefined amount of gas from the transaction’s gas limit.
- Operations manipulate the stack, memory, or storage according to their function.
- The program counter advances, and execution continues until reaching a STOP, RETURN, or REVERT opcode.
- State changes made during execution get committed if the transaction succeeds, or discarded if it reverts.
This process happens identically on every node. Deterministic execution is critical. Two nodes processing the same transaction must arrive at identical state changes, or consensus breaks down.
Consider a simple token transfer. The bytecode checks the sender’s balance, verifies they have enough tokens, subtracts from their balance, adds to the recipient’s balance, and emits an event. Each of these steps translates to multiple opcodes that the EVM executes sequentially.
Gas Metering and Execution Limits
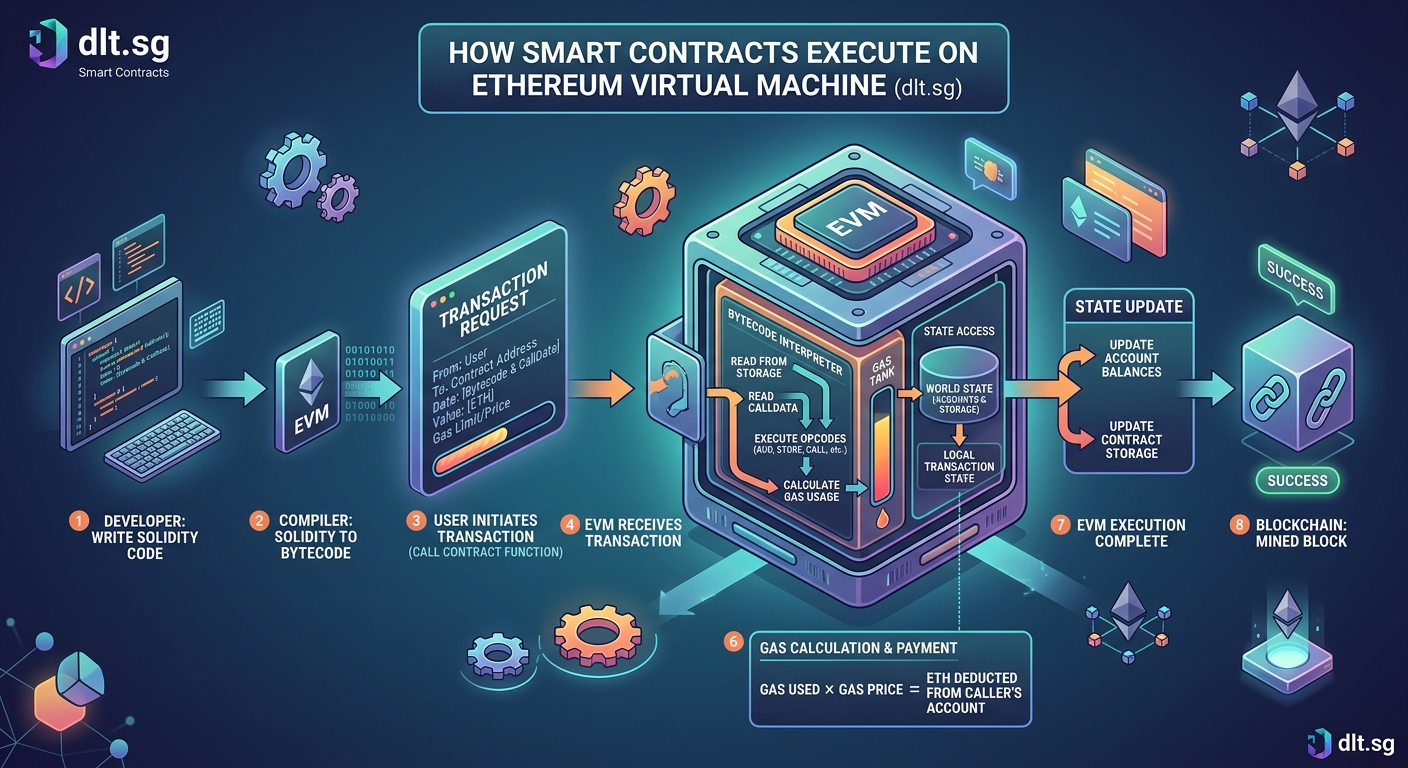
Gas is the fuel that powers EVM execution. Every opcode has a fixed gas cost.
Simple arithmetic operations like ADD cost 3 gas. Storage writes cost 20,000 gas for setting a new value, or 5,000 gas for updating an existing one. This pricing reflects the computational burden each operation places on the network.
What happens when you send a blockchain transaction? explains the broader transaction lifecycle, but gas metering happens at the opcode level during execution.
The EVM tracks remaining gas throughout execution. Before each operation, it checks whether enough gas remains. If not, execution halts with an “out of gas” error. All state changes revert, but the gas consumed up to that point is still paid to the validator.
This mechanism prevents infinite loops and ensures that every computation eventually terminates. Without gas limits, a malicious contract could lock up the network by running forever.
Gas costs also incentivize efficient code. Developers learn to minimize storage operations, reuse memory, and structure data carefully. A poorly optimized contract might cost users ten times more gas than a well-written equivalent.
Opcode Categories and Their Functions
The EVM supports around 140 opcodes, grouped into functional categories:
Arithmetic and logic: ADD, MUL, SUB, DIV, MOD, LT, GT, EQ, AND, OR, XOR, NOT
Stack operations: PUSH, POP, DUP, SWAP
Memory operations: MLOAD, MSTORE, MSTORE8
Storage operations: SLOAD, SSTORE
Control flow: JUMP, JUMPI, JUMPDEST, STOP, RETURN, REVERT
Environmental information: ADDRESS, CALLER, CALLVALUE, GASPRICE, TIMESTAMP
Block information: BLOCKHASH, COINBASE, NUMBER, DIFFICULTY
External interactions: CALL, DELEGATECALL, STATICCALL, CREATE, CREATE2
Each category serves a specific purpose in contract execution. Arithmetic opcodes perform calculations. Stack opcodes manipulate the working data. Storage opcodes read and write permanent state. Control flow opcodes implement conditional logic and loops. Environmental opcodes provide context about the transaction and blockchain state.
The CALL family of opcodes enables contract-to-contract interaction. When your contract calls another contract, the EVM creates a new execution context, loads the target contract’s bytecode, and begins processing. The called contract can modify its own state and return data to the caller.
DELEGATECALL is particularly interesting. It executes another contract’s code in the context of the calling contract, allowing library patterns and upgradeable proxy contracts. Understanding these interaction opcodes is essential for building complex decentralized applications.
State Changes and Consensus
Every opcode that modifies storage creates a state change. These changes are the whole point of smart contract execution.
The EVM maintains a Merkle Patricia tree structure for state. Each account has storage organized as a key-value mapping. When an SSTORE opcode executes, it updates this tree.
After executing all transactions in a block, nodes compute a new state root hash. This single hash represents the entire global state. If two nodes arrive at different state roots, they disagree about the outcome of transactions.
Understanding blockchain nodes covers node types in detail, but for smart contract execution, what matters is that every full node must compute identical state transitions.
This requirement drives many EVM design decisions. Floating-point arithmetic is forbidden because different hardware might produce slightly different results. Random number generation requires special handling because true randomness would break determinism. Time-based logic uses block timestamps rather than wall clock time.
State changes are atomic at the transaction level. Either all changes from a transaction succeed and get committed, or none do. There’s no partial execution state. This atomicity simplifies reasoning about contract behavior and prevents inconsistent states.
Common Execution Patterns and Pitfalls
Developers encounter recurring patterns and problems when working with EVM execution:
| Pattern/Issue | Description | Impact |
|---|---|---|
| Reentrancy | External call allows target to call back before state updates | Critical security vulnerability |
| Gas griefing | Caller provides just enough gas to fail partway through | Denial of service, wasted gas |
| Storage packing | Multiple variables in single storage slot | Reduced gas costs |
| Memory expansion | Accessing high memory addresses | Quadratic gas cost increases |
| Unchecked arithmetic | Operations overflow without reverting (pre-0.8.0) | Incorrect calculations |
| External call failures | Called contract reverts or runs out of gas | Transaction fails unless caught |
Reentrancy is the most famous execution pitfall. The DAO hack in 2016 exploited a reentrancy vulnerability where an external call happened before state updates. The called contract could recursively call back into the original contract, draining funds.
Modern contracts use the “checks-effects-interactions” pattern: verify conditions, update state, then make external calls. This ordering prevents reentrancy by ensuring state changes happen before any external contract can observe and act.
Gas griefing occurs when a caller intentionally provides insufficient gas for a subcall. The main transaction succeeds, but the subcall fails, potentially leaving the contract in an unexpected state. Defensive contracts check return values and handle failures gracefully.
Storage packing takes advantage of how the EVM stores data. Each storage slot holds 32 bytes. If you declare a uint8 followed by another uint8, the compiler can pack both into a single slot, saving gas on storage operations.
The EVM doesn’t care about your intentions. It executes opcodes exactly as written. A single incorrect assumption about execution order, gas costs, or state visibility can create vulnerabilities. Always test contracts thoroughly and consider professional audits for production deployments.
Debugging and Tracing Execution
Understanding execution becomes critical when contracts behave unexpectedly.
Several tools help developers see inside the EVM:
Remix debugger: Step through transactions opcode by opcode, viewing stack, memory, and storage at each step.
Hardhat console.log: Emit debug messages during local testing (stripped in production).
Tenderly: Trace production transactions visually, showing state changes and gas consumption.
Etherscan: View input data, internal transactions, and event logs for any transaction.
Transaction traces reveal the exact execution path. You can see which functions were called, what values were passed, where gas was consumed, and why a transaction reverted.
For complex failures, traces show the call stack. If contract A calls contract B which calls contract C, and C reverts, the trace shows the entire chain and the revert reason.
Gas profiling helps optimize contracts. By examining gas usage per opcode, you identify expensive operations. Maybe a loop iterates too many times. Maybe you’re reading the same storage slot repeatedly instead of caching in memory.
Why Solidity remains the dominant smart contract language in 2024 discusses language-level features, but debugging often requires dropping down to the bytecode level to understand what the EVM actually executes.
Advanced Execution Concepts
Beyond basic execution, several advanced concepts affect how contracts run:
Precompiled contracts: Special addresses (0x01 through 0x09) implement cryptographic operations in native code rather than opcodes. These include ECRECOVER for signature verification and SHA256 hashing. They execute faster and cheaper than equivalent opcode implementations.
Transient storage: Introduced in recent upgrades, this provides temporary storage that persists during a transaction but doesn’t get written to permanent state. It’s cheaper than regular storage and useful for reentrancy locks and temporary flags.
Code size limits: Contracts cannot exceed 24 KB of deployed bytecode. Large contracts must split functionality across multiple contracts or use proxy patterns.
Call depth limits: The EVM limits call stack depth to 1024. Deeply nested contract calls eventually fail. This prevents stack overflow attacks but requires careful architecture for complex systems.
Static calls: The STATICCALL opcode executes code without allowing state modifications. It’s used for view and pure functions, enabling optimizations and guaranteeing read-only behavior.
These mechanisms shape how developers structure applications. The code size limit encourages modular design. Precompiled contracts make certain operations practical that would be prohibitively expensive in pure opcodes. Transient storage enables new patterns for managing execution state.
Comparing Execution Across EVM-Compatible Chains
Ethereum’s execution model has been adopted by many other blockchains. Polygon, Binance Smart Chain, Avalanche C-Chain, and Arbitrum all run EVM-compatible environments.
This compatibility means smart contracts can deploy across chains with minimal changes. The same bytecode executes the same way regardless of which chain processes it.
However, subtle differences exist:
- Gas prices: Different chains have different base fees and congestion levels
- Block times: Faster blocks affect time-dependent logic
- Opcodes: Some chains add custom opcodes or modify costs
- Precompiles: Layer 2 solutions often add new precompiled contracts
Public vs private blockchains explores architectural differences, but for execution purposes, most EVM chains maintain high compatibility with Ethereum mainnet.
Developers building multi-chain applications must test on each target chain. A contract that works perfectly on Ethereum might behave differently on a chain with 2-second block times versus 12-second blocks.
Practical Execution Optimization Strategies
Writing efficient contracts requires understanding execution costs:
- Minimize storage operations: Read once, cache in memory, use local variables
- Pack storage variables: Group small types to fit in 32-byte slots
- Use events instead of storage: Off-chain indexers can track events cheaply
- Avoid loops over unbounded arrays: Gas costs grow linearly with iterations
- Mark functions as view or pure: Enable compiler optimizations and static calls
- Use immutable and constant: Set values at compile/deploy time instead of storage
- Batch operations: Process multiple items per transaction when possible
These optimizations directly reduce opcode count and gas consumption. A function that reads the same storage slot five times wastes gas. Reading once and storing in a local variable uses cheaper stack operations for subsequent accesses.
Events are particularly useful. They cost much less than storage writes but still get recorded on-chain. Applications can reconstruct state by replaying events, avoiding expensive storage reads.
Building your first dApp covers practical development workflows, including testing and optimization techniques that help you write execution-efficient contracts.
Security Implications of EVM Execution
Understanding execution mechanics is fundamental to security.
Many vulnerabilities stem from misunderstanding how the EVM processes opcodes:
- Integer overflow: Pre-Solidity 0.8.0, arithmetic wrapped around silently
- Reentrancy: External calls transfer control before state updates
- Delegatecall injection: Malicious libraries can hijack contract storage
- Gas manipulation: Relying on gas limits in logic creates attack vectors
- Block timestamp dependence: Miners can manipulate timestamps slightly
7 critical vulnerabilities every smart contract auditor looks for examines these issues in depth, but the root cause is always the same: developers making incorrect assumptions about execution behavior.
The EVM executes exactly what the bytecode specifies. It doesn’t infer intent or add safety checks beyond basic gas metering. If your code has a logical flaw, the EVM will faithfully execute that flaw every time.
Testing on local networks helps catch obvious bugs, but subtle execution issues often only appear under specific conditions. Fuzzing, formal verification, and professional audits provide additional safety layers.
How Execution Connects to Consensus
Smart contract execution and blockchain consensus are tightly coupled.
Every validator must execute transactions identically. The EVM’s deterministic design makes this possible. Given the same bytecode, input data, and blockchain state, execution always produces the same output.
Why do blockchains need consensus mechanisms? explains the broader consensus picture, but for smart contracts specifically, execution determinism is what allows thousands of independent nodes to agree on state changes.
If the EVM allowed any non-deterministic behavior, nodes would compute different state roots. The network would fork, splitting into incompatible chains. Every design decision in the EVM prioritizes determinism over flexibility.
This is why the EVM lacks features common in traditional programming environments. No system calls. No file access. No true randomness. No floating-point math. These restrictions ensure that execution depends only on blockchain state and transaction data, both of which are identical across all nodes.
The Execution Model’s Evolution
The EVM hasn’t remained static since Ethereum’s launch.
Network upgrades have added opcodes, modified gas costs, and introduced new execution features. The Berlin upgrade repriced certain opcodes based on real-world usage patterns. London introduced the BASEFEE opcode. Shanghai added transient storage opcodes.
Each change aims to improve efficiency, security, or functionality while maintaining backward compatibility. Existing contracts continue executing correctly even as the underlying execution environment evolves.
Future upgrades will continue refining the execution model. Proposals include verkle trees for more efficient state storage, statelessness to reduce node requirements, and execution sharding to increase throughput.
Understanding current execution mechanics provides a foundation for adapting to these changes. The core concepts of bytecode, opcodes, gas metering, and deterministic state transitions will remain fundamental even as implementation details evolve.
Making Execution Knowledge Practical
Theory becomes valuable when applied to real development work.
Understanding how smart contracts execute on Ethereum helps you write better code. You’ll structure contracts to minimize gas costs. You’ll avoid patterns that create security vulnerabilities. You’ll debug issues faster by reasoning about execution flow.
When a transaction fails, you’ll know how to trace execution and identify the failing opcode. When gas costs spike, you’ll understand which operations are expensive and how to optimize them. When building complex interactions between contracts, you’ll anticipate how call contexts and state changes propagate.
This execution knowledge also helps you evaluate other developers’ contracts. Reading bytecode becomes possible. Auditing for common vulnerabilities becomes systematic. Assessing gas efficiency becomes quantitative rather than guesswork.
The EVM is a simple machine at its core. It reads opcodes, manipulates a stack, and updates state. Everything else builds on these primitives. Master the fundamentals, and complex contract behavior becomes comprehensible.
Smart contracts execute predictably, deterministically, and transparently. Every operation is visible on-chain. Every state change is recorded. This transparency is blockchain’s superpower, but it requires understanding the execution model to use effectively.
Start experimenting. Deploy simple contracts on test networks. Trace their execution. Modify the code and observe how bytecode changes. Read other contracts’ bytecode to see how different patterns compile. The best way to internalize execution mechanics is hands-on practice with real contracts.
